

The CYFIRMA Industry Report delivers original cybersecurity insights and telemetry-driven statistics of global industries, covering one sector each week for a quarter. This report focuses on the Healthcare industry, presenting key trends and statistics in an engaging infographic format.
Welcome to CYFIRMA infographic industry report, where we delve into the external threat landscape of the healthcare industry over the past three months. This report provides valuable insights and data-driven statistics, delivering a concise analysis of attack campaigns, phishing telemetry, and ransomware incidents targeting healthcare, pharmaceutical and medical equipment manufacturing organizations and related services.
We aim to present an industry-specific overview in a convenient, engaging, and informative format. Leveraging our cutting- edge platform telemetry and the expertise of our analysts, we bring you actionable intelligence to stay ahead in the cybersecurity landscape.
The total number of 13 observed campaigns in the Healthcare industry is relatively small compared to other industries, like the finance or manufacturing and semiconductors industries. This aligns with the known low interest of many financially motivated groups, as it attracts unwanted attention from law enforcement, due to the sensitivity of healthcare.

TA505, MISSION2025 and Russian bears are the most active threat actors targeting the healthcare sector. Notably, TA505 being a financially motivated APT is known to disregard the unwritten rule of avoiding healthcare vicitms.

Nearly half of the targeted victims are from the European Union and the United Kingdom, followed by anglophone countries; USA, Canada, Australia and New Zealand. This is no surprise as they are collectively leading the world healthcare industry.
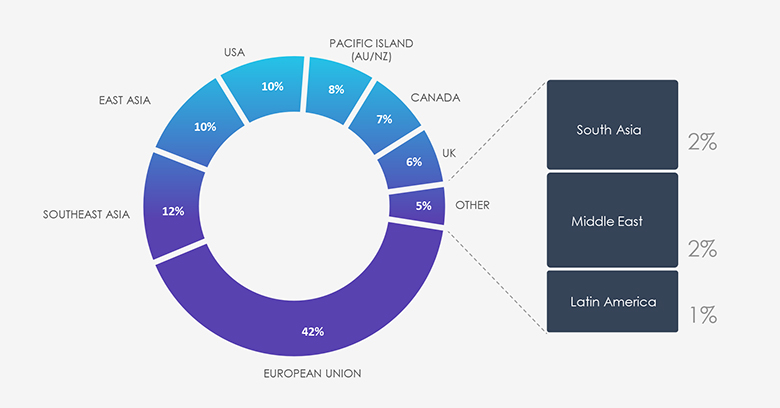
Due to the overlapping nature of monitoring telemetry, further breakdown is calculated for regions rather than individual countries to maintain clarity. Africa and Central Asia had no observed victims in this time period.
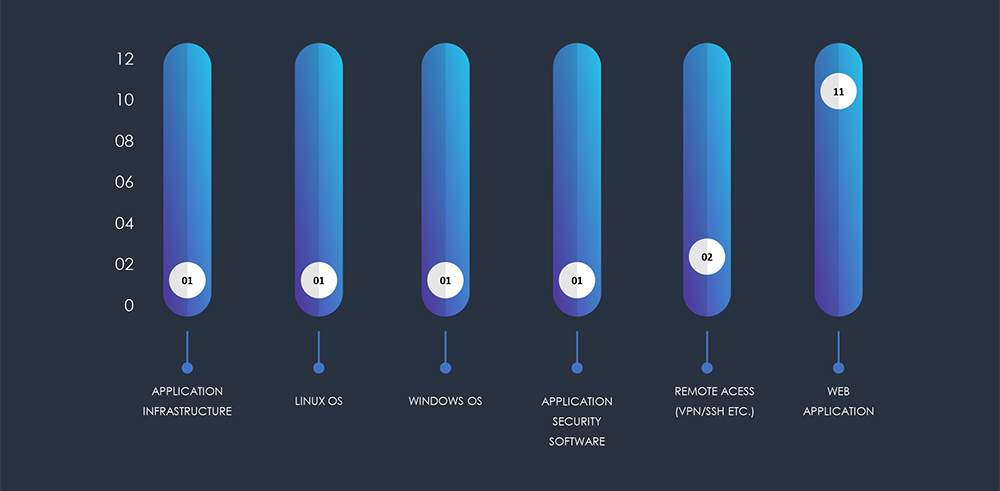
Analyzing the technologies targeted by APTs show a clear emphasis on exploiting vulnerabilities within web applications by a large margin, further focusing on remote access technology and weaknesses in Operation Systems.
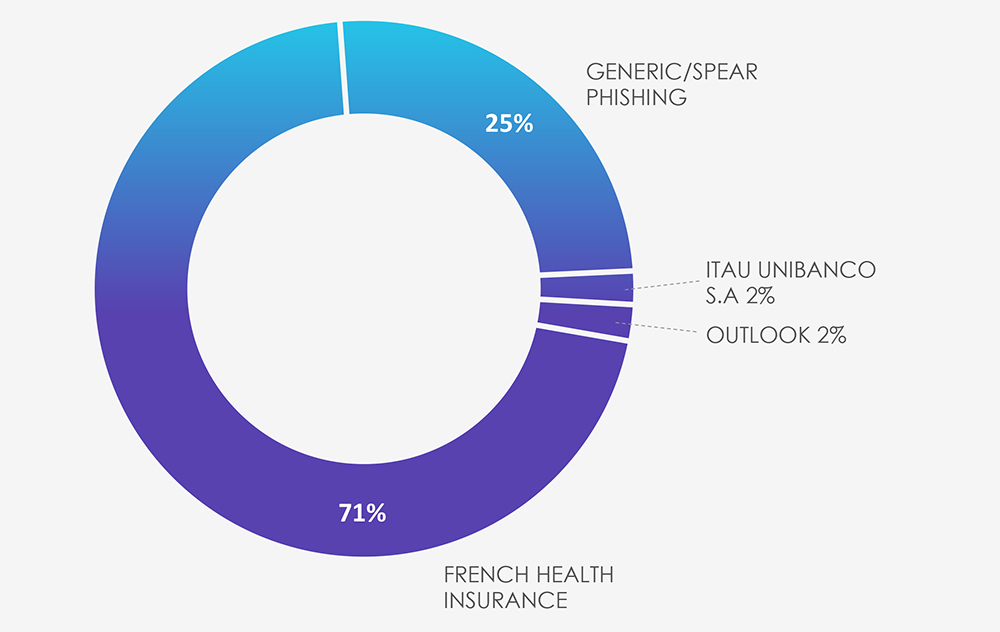
Phishing attacks explicitly targeting or impersonating the healthcare industry are very rare compared to other sectors. In the past 3 months, CYFIRMA’s telemetry observed only 135 out of total 105,930 phishing attacks involving the healthcare sector. This constitutes about 0.13% of all observed phishing attacks.
Due to the limited volume of healthcare-related observed campaigns and the ASN- based-origin geography, there is not much of a big picture. For the most part, ASN origin corresponds with a targeted or impersonated organization.
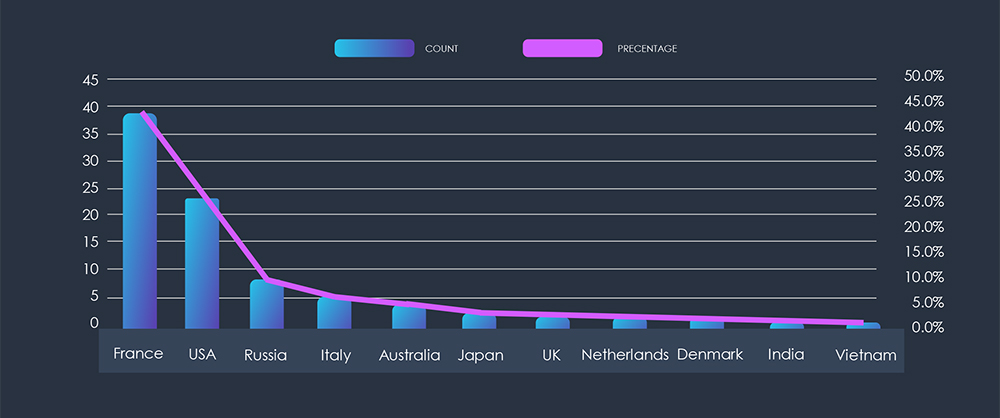
The only healthcare-impersonated organization observed is French Health Insurance, followed by a scattered generic phishing, including Italian Bank and Outlook application-themed phishing against healthcare organizations from various origin countries.
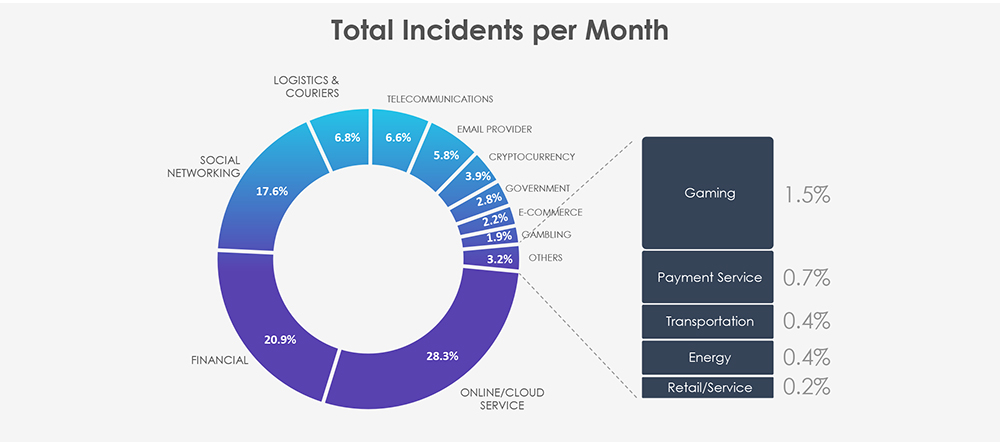
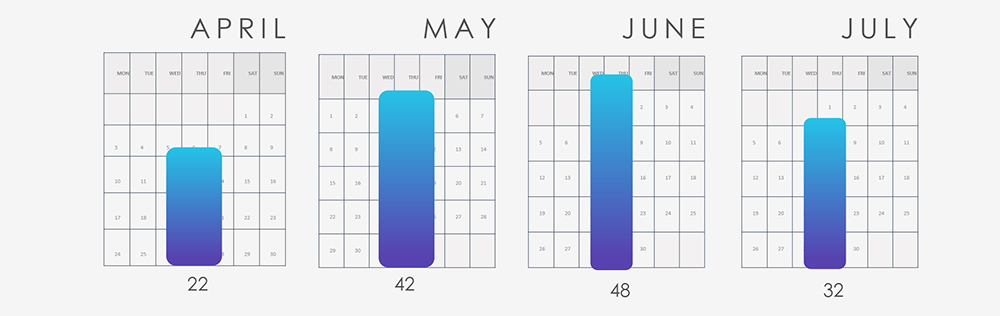
Over the last 90 days, CYFIRMA observed 144 verified ransomware victims from various healthcare sectors, out of the overall total of 1382 incidents, accounting for 10.4% of all ransomware victims during the same period.
The total number of incidents per month appear to be about even, not suggesting any remarkable trends within the last 90 days.
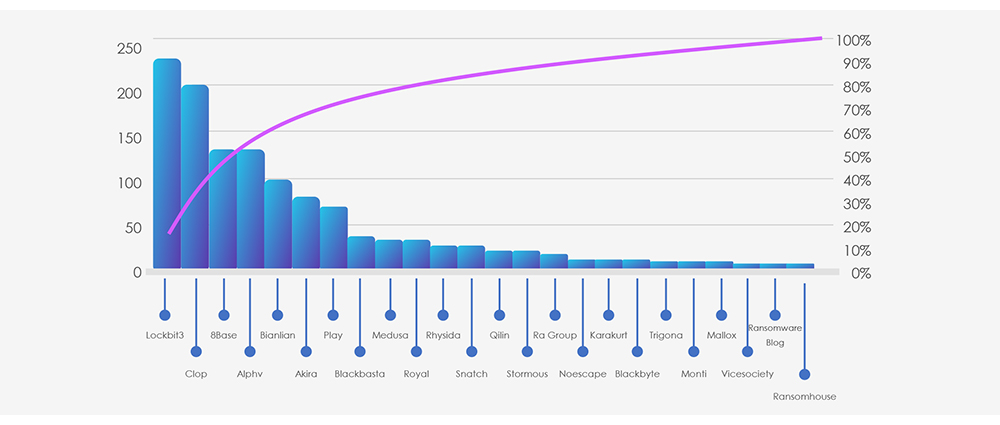
Incidents distribution per group shows roughly the same distribution as the wider threat landscape. Large groups are behind the largest number of attacks. However, it is interesting to see, that some large gangs like Play have minimum healthcare victims.
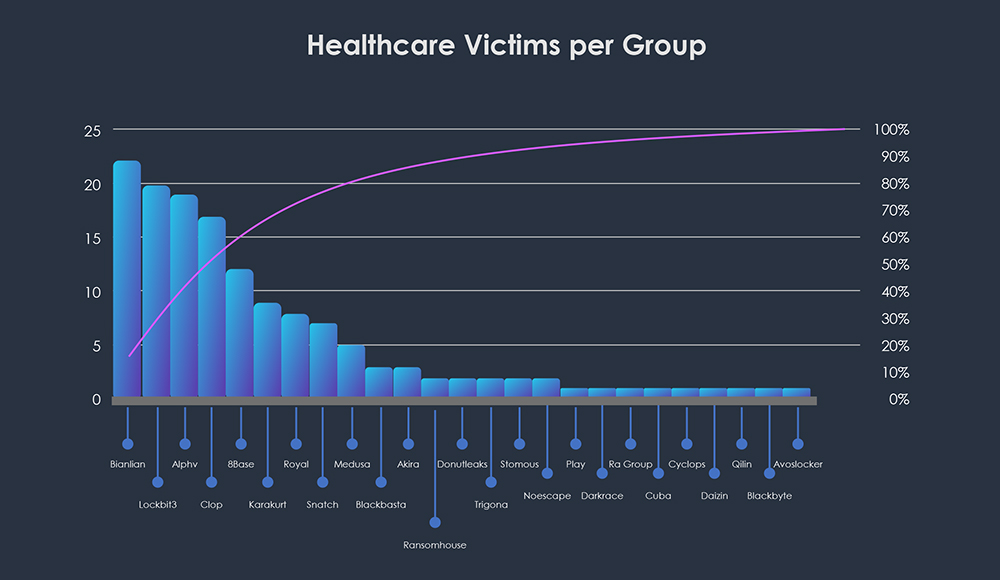
For quick comparison, below is a chart with a total count of victims, per top 25 ransomware groups, within the last 90 days.
A chart of activity per month for each group provides a more detailed insight into how the number of total incidents past 90 days remained even about each month.
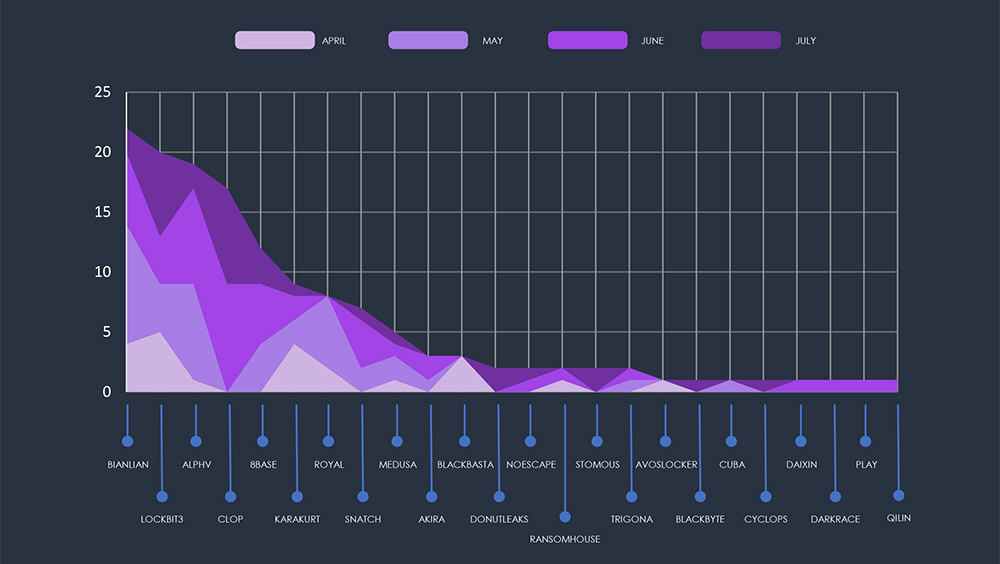
For example, Lockbit3 and ALPHV have consistent numbers across months, but Cl0p has no victims in healthcare during April and May, accounting for all their victims in June and July.
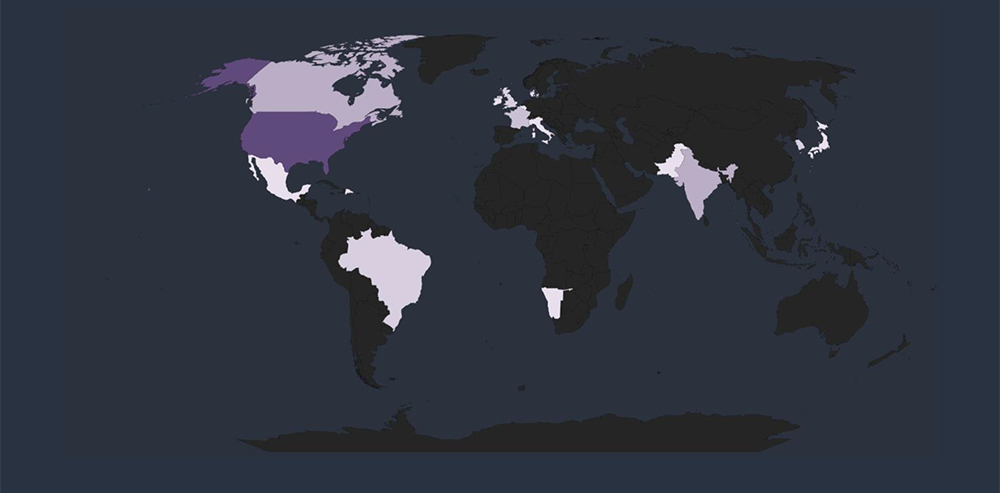
With 106 known incidents, the United States is the by far the most affected by ransomware attacks in the healthcare industry. This affirms that the US remains a prime target across industries, due to its economic significance and digital infrastructure.
Global Spread – Remaining known incidents with known victim countries are Canada (4 victims), India (4 victims) and France (3 victims). This correlates with a broad threat landscape across industries. Notable is India among the top 5 countries with their robust drug manufacturing industry.
The distribution of ransomware incidents in the past 90 days was observed across multiple sectors. The sectors that experienced the highest impact were Medical Services (43%), Pharmaceuticals (10%), Medical Devices (9%), Manufacturing (8%), and Healthcare IT systems (6%).
Vulnerable sectors – Medical services; Hospitals and Clinics together with the Manufacturing of Medical devices and pharmaceuticals, experienced the highest number of incidents, due to the known and common vulnerabilities, specifically against ransomware.
Broad targeting beyond the hardest hit sectors, like medical education, IT systems and medical billing implies an opportunistic approach within the Healthcare sector.

The healthcare industry is largely avoided by threat actors as it attracts unwanted attention from law enforcement. This is illustrated by barely existent phishing attack campaigns.
Exception to a rule are cybercriminals operating from Russia, where they are essentially untouchable by foreign law enforcement. And with the ongoing war, they hold no bars, even against targeting hospitals.