


Key Intelligence Signals:
Gamaredon Resumes Attack Against Ukraine
Summary:
Gamaredon is a Russian state-sponsored advance persistence threat group operating for a long time. Gamaredon was very active the previous year after the war broke out between Russia and Ukraine. To bypass security measures the group constantly changes malicious code with time. In recent attacks, the threat actor tried to deliver malicious documents via spear phishing attacks. The threat actor dropped a mail on behalf of a company whose background is in aerospace technology. The mechanism exploits remote template injection vulnerability (CVE-2017-0199) that leads to bypassing Microsoft Word macro protections to hack target systems with malware. On execution, it fetches the specified address and downloads the next stage of the attack chain. The threat actor employed such a mechanism that the payload was delivered only to targets with a Ukrainian IP address. If it is a Ukrainian IP address, it will drop a heavily obfuscated VBA script. The VBS is ordered to connect to a hardcoded Telegram account and to get instructions in a slightly obfuscated format leading to a new malicious IP address.
Insights:
Their mechanism to deliver the payload in a restricted geo-location shows the hard work they are putting into the attack. At the same time, it hints that Russia doesn’t want to target any other country which could bring bitterness to their relationship.
The leader of Russian foreign intelligence, which also encapsulates some of the top cyber capabilities in Russia, has noted that relations between Russia and China’s intelligence services are at an unprecedented level. The comments came from Sergey Naryshkin, viewed by many analysts to be the second most powerful man in Russia, who is the head of the Russian Foreign Intelligence Service. “We have a lot of interaction, and a large volume of intelligence, operational, and awareness information is exchanged,” Sergey Naryshkin, head of the Russian Foreign Intelligence Service, said at a news conference in Moscow. This is likely to include the exchange of know-how on Asian cyber operations, defenses, capabilities, and possibly even cooperation in cyber espionage.
The Russian economy is hit hard by the Western sanctions and is increasingly missing key imports of double-use goods, which fall under the sanction regime. While the Russian state is able to run a parallel import scheme, the quantities of goods and services obtainable in a clandestine way are limited, and Russian state TAs are likely to be tasked to gain access to the intellectual properties of Western or Japanese companies. The comments are coming in at a time of the uncertain position of the Russia-China partnership; While China is yet to deliver any substantial material support, it is likely to cooperate with Russia in the deniable cyber realm.
Russia’s private military corporation Wagner Group, headed by a henchman of President Putin and Russian troll factory operator Yevgeny Prigozhin, has recently sponsored a hackathon, with the state goal of contributing to the “development of IT projects to protect the interests of the Russian army.” The hackathon has been attended by numerous known cyber criminals which serve as another example of the Kremlin using cyber criminals as auxiliaries to promote its foreign policy interests. One of the winners of the hackathon was Igor Turashev, who is wanted by the FBI for his involvement with, among other things, Dridex banking malware and conspiracy to commit fraud leading to financial losses in the tens of millions of dollars. The Wagner PMC group, despite private military companies being technically illegal in Russia, opened a large company HQ in eastern St. Petersburg in November 2022. The center’s mission is “to provide a comfortable environment for generating new ideas in order to improve Russia’s defense capability, including information.” Analysts speculate that the deep coffers of the company, being financed by fraudulent deals of other Yevgeny Prigozhin’s companies with the Russian state, might enable the formation of a new and capable de facto Russian state APT, which could be easily used in the interest of the Kremlin.
Ukraine has signed an agreement to join NATO’s Cooperative Cyber Defence Centre of Excellence (CCDCOE). The center is based in Tallinn, Estonia, a small Baltic country that is the European champion of digital governance and that has suffered large-scale Russian cyber-attacks since 2007. Ukraine’s membership is expected to become reality soon, as no NATO country publicly objected to its accession. Closer cooperation is seen as benefiting both Ukraine and NATO as both parties can draw on different experiences in promoting best practices.
In other news, Ukraine’s State Service of Special Communication and Information Protection has recently estimated that Russian cyberattacks have risen threefold and that in some cases, cyber-attacks are launched in support of kinetic weapons, in an attempt to create a combined arms effect. This is a clear sign of Russia attempting to integrate cyber operations and information operations with missile strikes and action on the ground in its military doctrine.
The agency has recently released a report “Cyber Attacks, Artillery, Propaganda. General Overview of the Dimensions of Russian Aggression” which stresses signs that Russian attempts at coordinated operations have increased and that the attacks have generally been parried by Ukrainian defenses, but they remain an enduring threat.
CYFIRMA Research team observed that Ransomware attack results in the theft of data from Yum! Brands, the fast-food brand operator of KFC, Pizza Hut, Taco Bell, and The Habit Burger Grill fast-food restaurant chains in the United Kingdom. The ransomware attack forced the closure of 300 locations in the country.
Yum! Brands operates 53,000 restaurants across 155 countries and territories, with over $5 billion in total assets and $1.3 billion in yearly net profit.

Source: Telegram
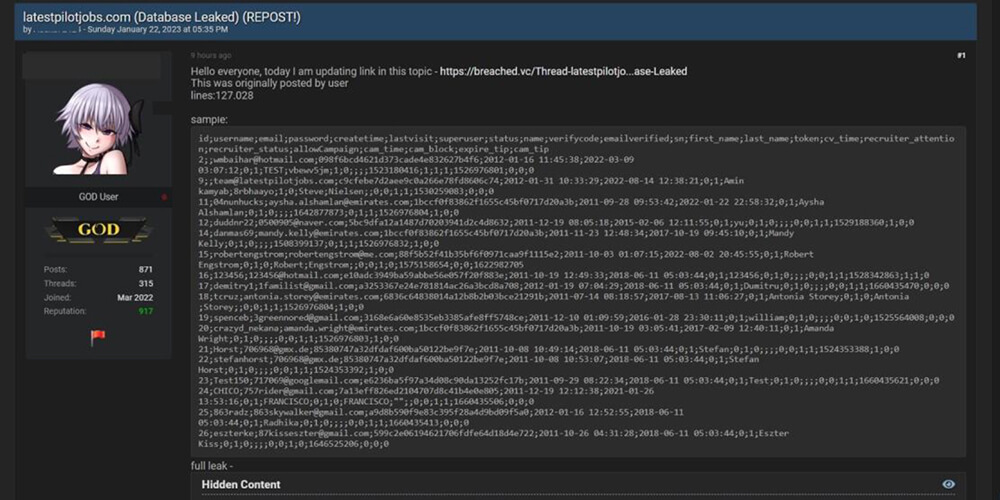
Source: Underground Forums