


Key Intelligence Signals:
North Korean APT BlueNoroff Unleashes Fresh Attack & Evades MOTW Protection
Summary:
In a recent development, researchers uncovered cyber-attack campaigns launched against companies in various countries like the USA, UAE, Taiwan, and Japan. The threat actor is attacking with the sole purpose of financial gain, in past, the group had successfully compromised crypto targets and disappeared after stealing cryptocurrency. BlueNoroff is a subgroup of Lazarus group, that was seen delivering Visual Basic Script, a previously unseen Windows Batch file, and a Windows executable in recent campaigns. In a fresh attack, researchers observed malware with slight changes that bypassed Mark-of-the-Web windows protection. One of the victims from UAE received a malicious document that connects to the remote server and downloads the payload. In this case, the executable ieinstal.exe was used to bypass UAC. Upon infection, the threat actor executed several Windows commands to gather basic system information. They, then returned 18 hours later to install further malware with high privileges.
More than 70 domains were weaponized, which looked like venture capital and bank domains. Several domains were copies of Japanese venture capital companies, hinting that the group had more focus towards targeting Japanese financial entities.
Insights:
MOTW is a mitigation technique introduced by Microsoft. The threat actor developed malware to bypass MOTW
New finding shows, actor has introduced slight modifications to deliver their malware, which also hints towards more incoming targets.
Summary:
Kimsuky has been active since 2012, known for targeting think tanks, national security, foreign policy, and journalists across the Korean Peninsula. In the recent campaign, the threat actor dropped spear phishing emails from multiple email accounts impersonating governmental figures in Korea. The target was a journalist associated with the 20th Presidential Transition Committee in April, a secretary from the office of Tae Yong-ho of the ruling People Power Party in May, and an official from the Korean National Diplomatic Academy in October.
All emails had an attachment of a link to a fake website or an attachment carrying malware. As part of operation security, threat actors used IP addresses from compromised servers. The attackers consumed over 326 servers across 26 countries, 87 of which belonged to organizations within Korea.
Insight:
As per the report, the targeted individuals were part of diplomacy, defense, and security.
General Paul Nakasone, the chief of Army Cyber Command and director of the National Security Agency, said that his command conducted both offensive and defensive operations in the lead up to the 2022 U.S. midterm elections. In 2018, US military hackers conducted cyber-attacks to protect U.S. networks and disrupted the Russian troll farm known as Internet Research Agency, run by President Putin’s close aide Yevgeny Prigozhin, known also for his role as proprietor of Russian private army Wagner PMC. In 2020, the cyber command disrupted Iranian influence operations, in which Iranian agents posed as members of the far-right group Proud Boys in an attempt to upset and sway American voters. General Nakasone wouldn’t say who the 2022 operations were aimed at or what kind of action the Cyber Command took specifically. Nakasone said that Cyber Command saw fewer threats against the midterm election than it had in the past, likely because of unrest in Russia, Iran, and China.
KillNet, the hacktivist auxiliary of the Russian government and a very active actor in cyberspace during the Russian war in Ukraine, has turned its attention to healthcare. The US Department of Health and Human Services, through its Health Sector Cybersecurity Coordination Center (HC3) has warned US hospitals and other healthcare providers that they should expect to receive attention from Russian hackers, with specifically pointing out KillNet. KillNet has previously targeted, or threatened to target, organizations in Healthcare and while most attacks disrupted record keeping or threatened data confidentiality, KillNet has threatened to compromise medical devices as well.
The group, most known for launching coordinated distributed denial-of-service (DDoS) attacks, targeted multiple counties supporting Ukraine in the recent months and while the majority of its activity has been on the nuisance level in the government sector and its threats should be taken with some reservations, the group still represents a real threat.
The government information security agency of Poland (Government Plenipotentiary for the Security of Information Space) warned over the weekend that Russian cyberattacks against third-party countries that have supported Ukraine during Russia’s war can be expected to increase. Russian hackers have targeted Polish transportation infrastructure with Prestige malware last fall and Russian activity has been observed in critical infrastructure and energy installations in numerous Western countries during last year. The agency stated, “Hacker groups linked to the Kremlin use ransomware, DDoS and phishing attacks, and the goal of hostile actions coincides with the goals of a hybrid attack: destabilization, intimidation and sowing chaos.”
According to media reports, Portugal’s Port of Lisbon sustained a ransomware attack. The extent of the attack is not clear, though port officials stated that operational activity was not compromised. Responsibility has been claimed by LockBit, a notorious ransomware gang, who also claims to have stolen financial data, cargo, crew and customer information or email correspondence. The gang is threatening to publish the stolen data if the ransom isn’t paid in time.
European ports were recently singled out by US cyber officials as potential weak points in European defense, as a lot of defense logistical chains depend on maritime shipping of weaponry from mainland US, which is manifested in the current conflict Russia is waging on Ukraine. A potential cyber-attack on the German ports of Bremerhaven or Hamburg would severely impede NATO efforts to send military reinforcements to allies. The attack on the port of Lisbon seems to be a purely criminal endeavor. However, the attackers might have gained potentially sensitive data, as Portugal is a founding member of NATO, and its infrastructure has historically been used by the US military.
CYFIRMA Research team observed threat actors selling multibillion-dollar insurance company VPN, Admin, and Root access. This access was sold for 360,000 USD.
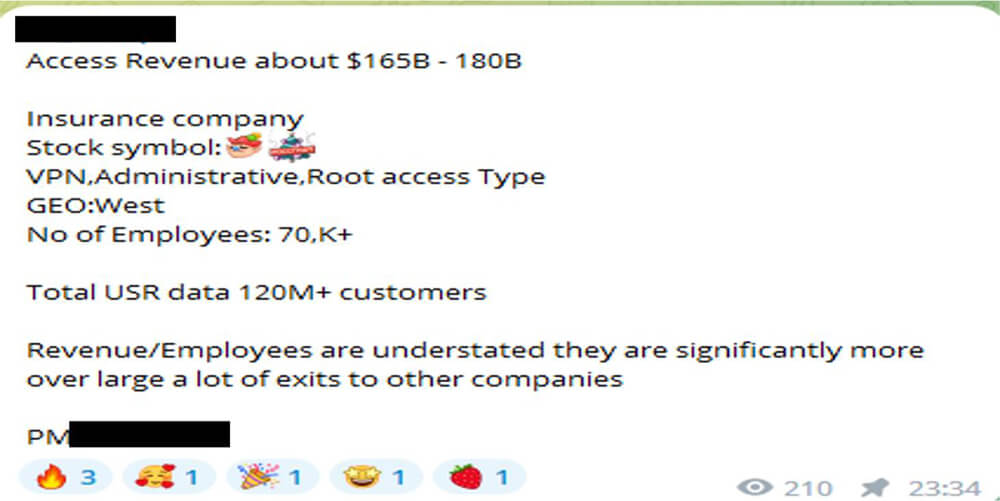
Source: Telegram
According to Japanese media reports, the police of this country have succeeded in decrypting encrypted data using Lockbit ransomware. The description and method of this work has not been published. In response to this news, LockBit’s spokesperson called this news a rumor of yellow magazines and announced that this is old and related to version 2 of LockBit.
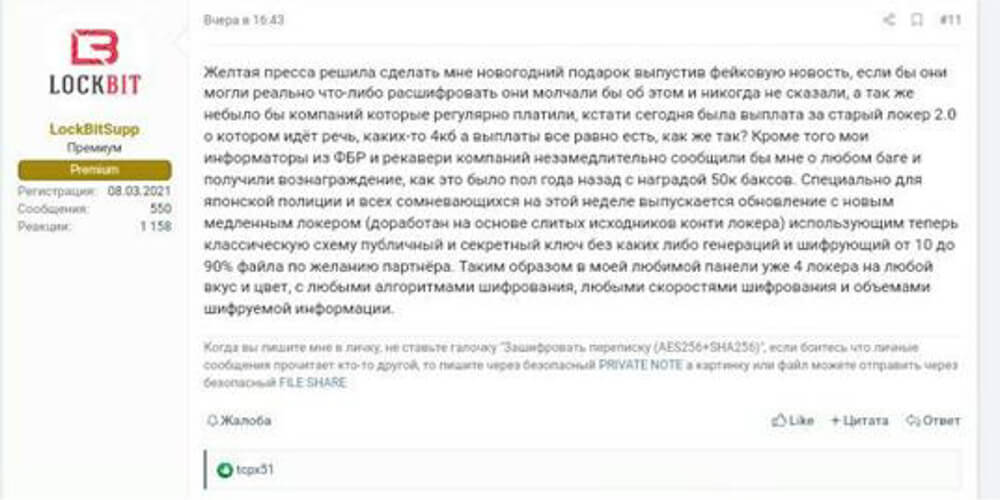
Source: Underground forum
Ever since the Twitter DB information leaked, it has been a field day for SIM swappers and scammers. We obseraved several celebrities’ accounts getting compromised.
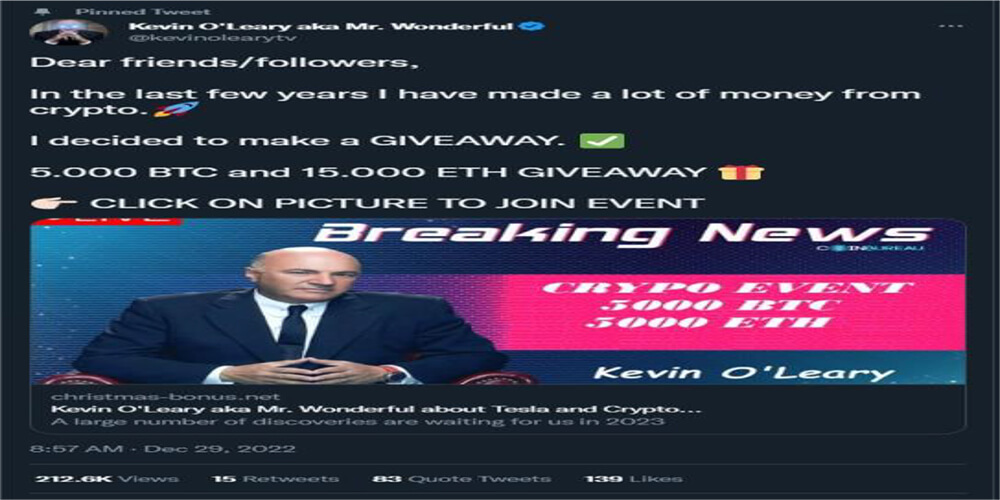
Source: Twiter
Inidia Railways 30 Million user data was advertised for sale in underground forum.
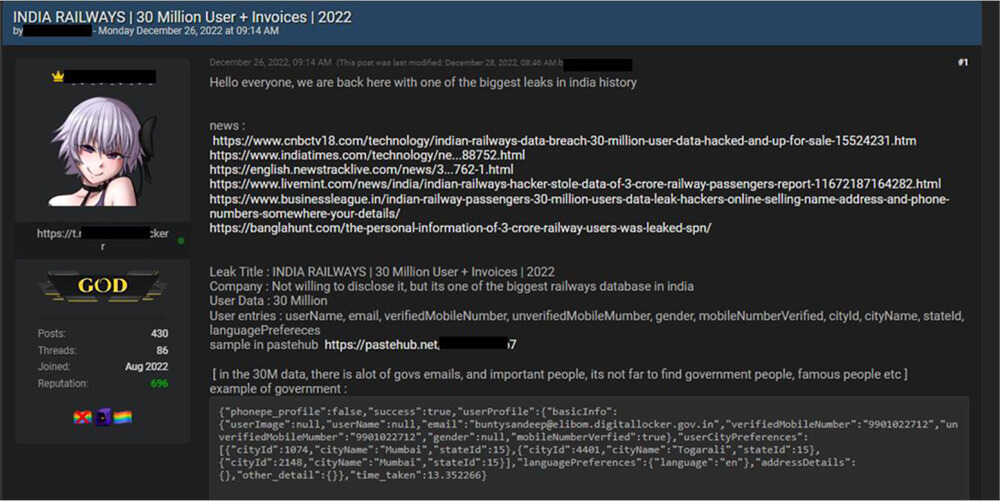
Source: Underground Forums
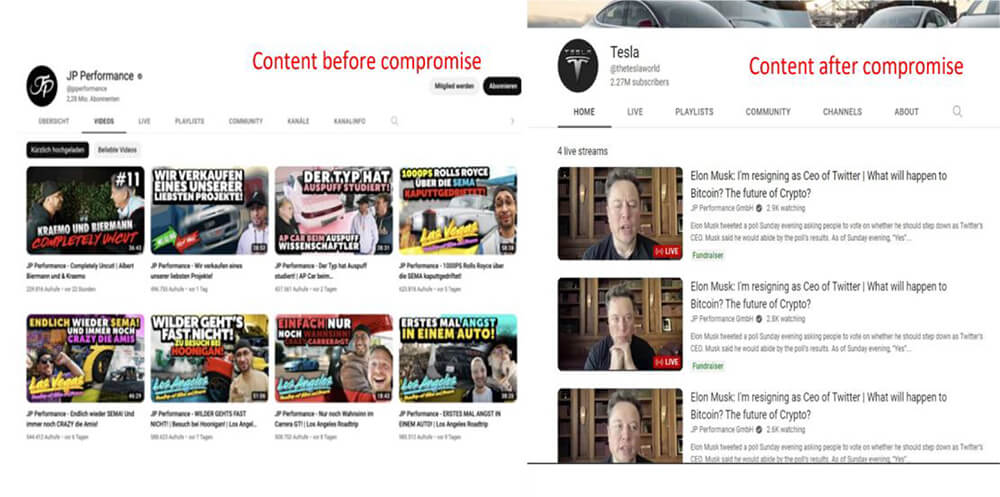
JP Performance GmbH, a large German YouTube channel with over 2,270,000 followers has been compromised. The YouTube account has changed its name to “TheTeslaWorld” and is actively pushing a Bitcoin scam. Threat actors possibly target corporate-backed social media accounts to conduct their cybercrime activities. Corporations need to strengthen their security; to protect their social media accounts; to avoid reputational damage.
Source: Telegram